Cryptosystems are designed to cope with the worst case scenarios: an adversary with infinite computing resources can get access to plaintext/ciphertext pairs (and thus could study the relationship between each pair) and knows the encryption and decryption algorithms; so can choose plaintext or ciphertext values at will.
The only element not accessible to this adversary is the secret key; thus the security of a cryptosystem depends solely on the security of the key. This is a long-standing design philosophy first enunciated by Auguste Kerckhoff in 1883 which states: “The security of a cryptosystem must not depend on keeping secret the crypto- algorithm. The security depends only on keeping secret the key.”
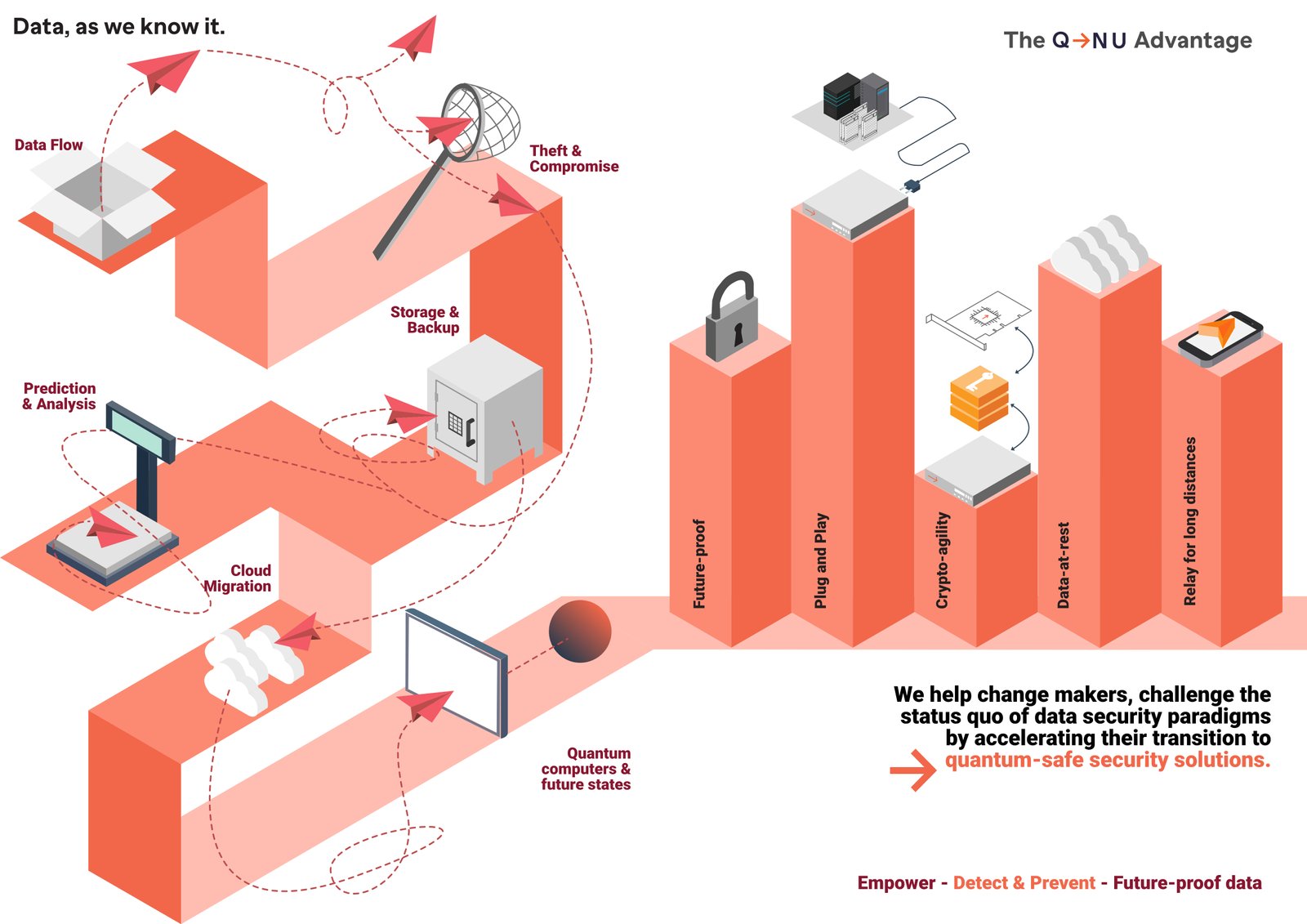
Today’s encryption (secret) keys are highly vulnerable due to many reasons such as weak randomness, advances to CPU power, new attack strategies, emergence of new algorithms such as Shor’s, which when run on quantum computers will ultimately render much of today’s encryption unsafe. Some of the recent news and disclosures has shown the stark reality and the ugly face of data security.
- Snowden disclosed in 2013 that Government Communications Headquarters (GCHQ), a British agency, has been copying 20 petabytes of data every day off optical fibers around the world under a secret project “Tempora” and had been giving the encrypted data to National Security Agency (NSA).
- A Reuters report in 2013 mentioned that NSA paid $10 million to put its backdoor in RSA encryption such that, the programme had a random number generator, but there were a number of fixed, constant numbers built into the algorithm that could function as a kind of skeleton key. Anyone who knows the right numbers can decipher the resulting crypto text.
- Another recent news with an interesting title, ‘The intelligence coup of the “century” shook the world. As per this news, for decades, the CIA and the West German intelligence have been reading the encrypted communications of over 60+ countries, including allies and adversaries for decades.
There are also echoes of crypto in the suspicions swirling around modern companies with alleged links to foreign governments.
While the bright side of powerful QCs will help solve a lot of problems for humanity and will give a huge boost to discovery of drugs, new materials and space research, at the same time the dark side of QCs will accelerate the maturation of the three of global top 10 risks, which are cyber-attacks, data theft or fraud and breakdown of information infrastructure. These global risks will create another sort of havoc by exposing and threatening the leakage of national defence secrets.
A particular concern is that data encrypted today can be intercepted and stored by state-sponsored hackers or other well-funded hackers for decryption in future by quantum computers. This is known as “Harvest Now Decrypt Later” attack.
Quantum safe technology needs to be adopted to safeguard the hacking of encryption keys. A technology that can address the practical difficulties such as generating long random keys, distributing keys to recipients, sender and receiver to be totally synchronised to make sure that the same keys are used for the same message, and ensuring that keys are never reused.
Quantum key distribution (QKD) is one such technology that addresses all of the above mentioned challenges. It is a key establishment and distribution protocol which creates a shared symmetric key material by using quantum properties of light to transfer information from Alice to Bob in a manner that will highlight any eavesdropping by an adversary. This can be used to derive a key, and the resultant key material can then be used to encrypt plaintext using a one-time pad encryption or using AES to provide unconditional security. QKD is especially good at creating long random keys from a short input – key extension functionality, which could be invaluable for OTPs.
QKD is a unique weapon in the cryptographer’s toolbox, albeit potentially powerful, empowering our defence and intelligence organisations with detection and prevention capabilities in case of any attempt of eavesdropping event. Defence can leverage the power of quantum secure solutions in the following applications:
- QKD for backbone bulk connectivity: Dynamic and effective key changes on important backhaul OFC links and even tactical bulk communication media in the field.
- Secure OFC ring networks: Development of static internet communication networks especially optical fibre ring networks in cantonments and other sensitive areas.
- Secure internet-based services: The growing dependency on internet-based service is a potential security threat and the use of strong encryption with QKD presents a viable solution.
- Generation of a large number of highly random keys: The keys must be truly random to be effective. True entropy can be achieved by using a quantum source for entropy, called ‘Quantum Random Number Generator’.
- Network-based encryption key distribution and management: Replacement of out-dated manual key management systems with real time key distribution and management using QKD.
QNu Labs is India’s one and only quantum secure communication company offering quantum safe internet and cloud security solutions. QNu Labs offers two products – Tropos (Quantum Random Number Generator) and Armos (Quantum Key Distribution System). These offerings make security of critical data unconditional and future proof. The company’s quest has been to offer crypto agility to organisations where the existing infrastructure can be upgraded to quantum secure in a seamless manner without any disruption in the business and any wastage of existing investments. QNu Labs has achieved this by replacing the vulnerable core of data security that relies on the complexity of mathematical algorithms with the unique principles of quantum physics.
QNu Labs is highly passionate and motivated about its mission of accelerating the world’s transition to quantum safe security solutions to protect critical data from an imminent Y2Q (Years to Quantum Computers) event, which will bring a ’crypto apocalypse’. The company was selected by MoD to present its unique offering in the India Pavilion of DefExpo 2020 and QNu Labs chose to showcase a use case of “Quantum Channel-based Real-time Key Distribution” along with BEL. The company saw a good footfall with some of the top Indian and foreign defence personnel visiting its booth and discussed the possible solutions of leveraging QNu’s technology to create a quantum safe secure network.
–The author is Co-founder and CEO, QNu Labs Pvt. Ltd.